It’s not hard to convince IT of the advantages of using multi-factor authentication. Those with a technical background know just how beneficial of a security control it can be for protecting systems from unauthorized access. However, making a business case to your executive team to fund the effort, and convincing your end users why they will have to go through another step before they are granted access to systems they use every day is often another story.
However, as hackers continue to evolve their strategies, phishing e-mails are becoming more difficult to identify, and a recent spike in successful phishing attacks is prompting many organizations to take additional steps towards implementing multi-factor authentication sooner than later.
Is your organization in the process of implementing multi-factor authentication on your systems? How have others before you successfully convinced employees to both accept and appreciate the extra steps the organization is taking to protect information? Keep reading for some of our best tips and things to consider if you choose to implement multi-factor authentication.
What is Multi-Factor Authentication (MFA)?
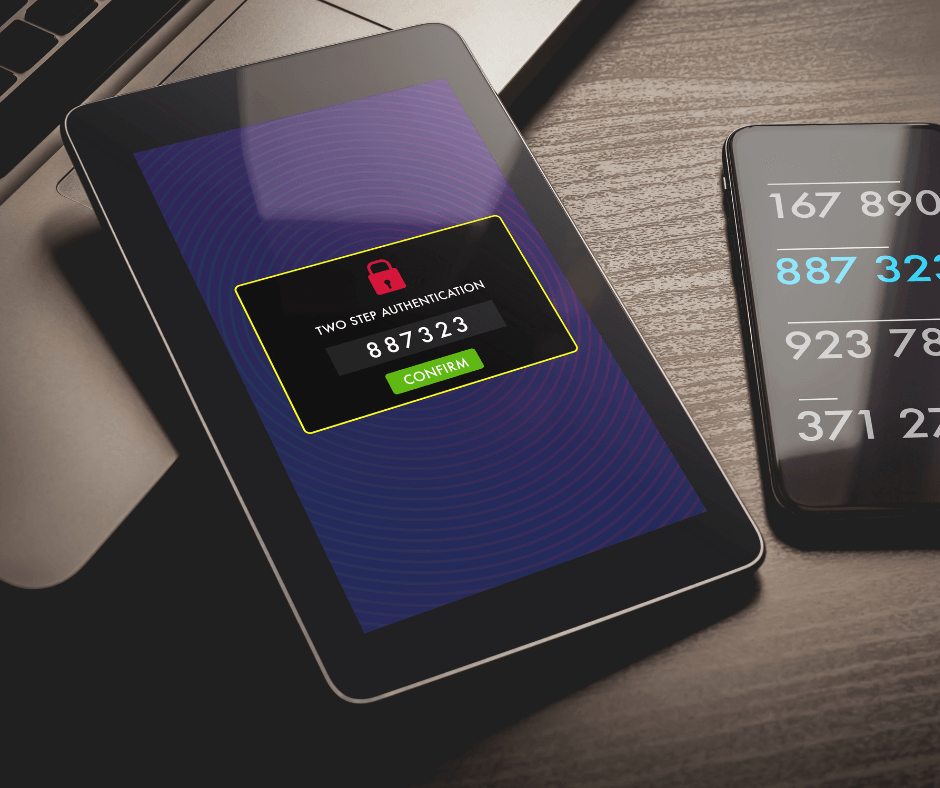
It is actually a fairly simple concept. MFA adds a second layer of security to help prevent anyone other than an authorized individual from gaining access to a secure system. Access requires two different types of authentication:
- Something you know – like your username and password
- Something you have – like a USB hardware token, or mobile device, phone, etc. that allows you to confirm your identity
- Something you are – biometrics like a fingerprint, retinal scan, or facial recognition
How does it work?
Even if hackers are able to successfully phish a login ID and password from a vulnerable user, or acquire passwords through installed malware, without that second factor, they are unable to successfully access a system that has MFA deployed.
Is MFA technically a requirement?
PCI DSS Requirement 8.3 states that organizations must secure all individual non-console administrative access and all remote access to the CDE using multi-factor authentication. This is a best practice until January 31, 2018, after which it becomes a requirement.
So, while it may not be required for other systems and users within your institution, it is recommended by most information security professionals. By implementing MFA, you can help mitigate the vulnerability caused by compromised access credentials almost immediately.
What solution is best for our organization? What criteria should be considered when evaluating vendors?
The most common and convenient forms of MFA include a mobile phone with a MFA application installed, a text message that is generated with a series of passcodes after the initial password is provided, or a phone call that allows you to authenticate that it is you who is attempting to connect. These solutions are relatively straight forward to implement, and are not overly difficult for end users to learn and utilize.
As more organizations have employed MFA, vendor options have increased, but with each come different benefits and problems. You will want to assess and understand your organization’s need, risks, and support capabilities before comparing solutions, so you can find the one that works best for you. Don’t automatically assume that an out-of-the-box solution will work for your environment. Verify all scope and implementation details to ensure the solution will integrate with your various applications.
Another factor to be considered when analyzing different solutions is always cost. On top of the direct costs like purchasing software or licensing, there can be other hidden costs involved. For example, you might need to take into account the cost of supplying and distributing hardware (e.g. tokens, smart cards, or biometric readers) or the logistical costs involved in the biometric enrollment process. Costs for added technical support staff must also be considered as you will probably see an increase in the number of support calls. People can’t remember their password, their token isn’t working, they left their phone at home, etc. One helpful trick we have learned from our customers is that you should always enroll new users during the first part of the week. That way, if they encounter any issues, support staff can get them resolved before the weekend.
What systems do we really need MFA on?
This will be an organizational, risk-based decision. If you have not already done so, do a proper risk assessment to determine what systems are accessing or storing sensitive information (e.g. PII or cardholder data) and what is the risk of exposure for each. You may decide to dip your toes in the water by focusing on your critical systems first. Or, you can dive in and roll it out across all organizational systems. Decide what approach is best for your environment and then develop a clear roadmap for implementation, so you can plan efficiently for communications, support staff, and initial and recurring costs.
While not required, we recommend that you consider rolling it out for all systems that house sensitive information. The real work is in the beginning while you are getting the process set up for the end users (activating tokens and/or smartphones will require some hand holding). Consider also including your email and LMS platforms due to the frequency with which these two systems are often targeted by hackers.
Outlining the Return on Investment (and Potential Costs of Doing Nothing)
Now that you have determined the best one or two solutions that will meet your organization’s needs and where you plan to implement MFA, you are ready to present your proposal for approval. Go in prepared and ready to outline exactly what the project will entail and how you plan to streamline the roll-out with the least impact on business as possible. Executives will want to see exact costs and know that you have done your homework to uncover any potential roadblocks prior to moving forward. You should also have references to back-up your request detailing what will happen if you don’t go down the path of multi-factor authentication. Current events are always helpful. “We don’t want to be the next Yahoo.”
Share that data breaches, no matter the size, do not come without significant costs. Damages caused by a breach can include:
- Exposure of personal information, intellectual property, or institutional information
- Loss of trust and significant reputational damage
- Expensive remediation costs and fines (average of $200 per compromised record)
Why continue to make your organization and employees easy targets when there is a solution out there that can help?
A Strategic Roll-out Can Save a Lot of Headaches
Once you have a selected a solution and been granted approval, there will be significant planning for the IT team. They will need to ensure your infrastructure is current. There may be different integrations with your Single Sign On processes, and they will be responsible for providing users with any necessary hardware or software upgrades.
But, once all of that preparation is complete, the real work comes in – how you are going to change user perceptions…?
You need to determine who is required to use MFA from your population of users (i.e. all staff, third-party contractors, temps, etc.)? If certain groups of users are more at risk, you might consider a phased roll-out. For example, all admin level staff is required to use MFA, other staff have the ability to opt-in. Sometimes this plan will allow users to feel more in control and allow a little time for acceptance to grow before you make it mandatory for all.
Make sure you also take into account those staff that use assisted technology, and have an appropriate access method ready.
If you are using smart phones or other mobile devices to prompt the second authentication, what is your policy going to be regarding lost or stolen devices? And are you going to have any alternative methods available for those that push back? Even if you don’t advertise that there are options available, you might want to purchase some hardware tokens for that small percentage of users that strongly oppose using their smartphones.
A solid and thoughtful communications plan is critical. Just as you did with the executive team, make the case for the risks of phishing, stolen credentials, and data breaches, and the expensive consequences that can follow. Stress that the threats are real, your organization is not immune, and that multi-factor authentication is a positive tool that is going to help protect everyone. Circulating an e-mail campaign and providing a website with more information and frequently asked questions can help educate users and steer away a lot of questions you might get down the road.
Work with managers or group leaders to win their support and help you sell the idea. During all of these awareness campaigns, however, make sure you are still linking back to your broader information security efforts – MFA is going to help a lot, but it does not address all risks, so users will still need to be vigilant.
Stay the Course!
You’ve spent all that time on your plan, you’ve communicated it to your users, now don’t sway from it. Strong support from leadership is essential and will be important for achieving buy-in from the rest of the organization. Continue to stress that multi-factor authentication isn’t just some silly constraint IT is pushing out to make their lives more difficult; it is designed to protect your employees, your customers, and your organization.
Some additional guidance from our Security Advisor team below:
[Gokturk]: If you were to ask anyone who has had their email or bank account compromised–due to any one of several malicious password stealing tools commonly used–whether they wish they could have enabled multi-factor authentication (MFA) for the accounts prior to compromise, and whether they are currently utilizing a multi-factor control to protect their accounts, they will respond with a resounding YES! It is common knowledge among security professionals that passwords alone are not sufficient to protect accounts. Fortunately, awareness among non-security professionals of the importance of multi-factor authentication is spreading. Unfortunately, it is often not until after a compromise occurs that multi-factor is implemented. When met with resistance due to the cost of implementation in an organization, consider asking why they would enable multi-factor authentication to protect their personal accounts and yet not apply the same level of protection to systems containing sensitive information entrusted to their organization by their customers? Not only is it a PCI DSS requirement, it is essential for protection against malicious actors who continuously work to find ways to steal passwords to gain access to information systems and networks.
If you have questions about how your organization should be deploying multi-factor authentication, don’t hesitate to reach out to us.

