
Cyber threats targeting energy and utility infrastructure are no longer a distant risk. They are a present and growing danger.
In response, the New York State Public Service Commission (PSP) now requires regulated utilities to treat cybersecurity as a legal duty, essential to providing safe and adequate public service.
What Is Case 25-M-0302?
On June 13, 2025, the New York State Public Service Commission issued an order instituting a proceeding to establish cybersecurity requirements for information technology under 16 NYCRR, formally known as Case 25-M-0302. Following a public comment period that closed September 15, 2025, the regulations were finalized and became effective January 1, 2026.
The proceeding was driven by a recognition that utilities are high-value targets for cyberattacks, prompted by a 2023 amendment to the Public Service Law requiring gas and electric corporations to develop tools to protect consumer privacy, and by Governor Hochul’s call to strengthen cybersecurity for the State’s water infrastructure.
The Commission’s core finding: “Adequate cybersecurity is now an intrinsic part of safe and adequate service.” Cybersecurity is no longer a best practice; it is a legal obligation embedded in the duty to serve.
The regulations establish a dynamic set of mandatory, minimum, and enforceable standards designed to be strong and agile enough to meet today’s threats, as well as those expected in the future.
The current phase focuses on Information Technology (IT) and the protection of Personally Identifiable Information (PII), with a separate proceeding planned for Operational Technology (OT).
Who Is Impacted?
The PSC anchored its authority in its longstanding supervisory power over public utilities, making these obligations broadly applicable across regulated utility sectors:
- Gas and Electric corporations
- Water-Works corporations
- Steam corporations
- Telephone corporations
- Cable Television companies
Exemptions: Municipal corporations and regulated entities generally serving fewer than 50,000 customers are exempt from coverage under these regulations.
What the Regulations Require
The draft regulations, now in effect, impose a comprehensive set of minimum, mandatory cybersecurity obligations on covered entities. Key requirements include that organizations:
- Designate a Chief Information Security Officer (CISO)
A qualified CISO must be designated to oversee and manage the organization’s cybersecurity program and enforce policy across all covered IT systems. - Establish a Formal Cybersecurity Program (§1200.2)
Covered entities must create and maintain a documented, risk-based cybersecurity program designed to proactively identify, mitigate, and respond to threats against IT systems and PII. - Adopt Written Cybersecurity Policies (§1200.3)
Entities must develop and maintain written policies governing data governance, access controls, system monitoring, and incident response protocols. - Conduct Ongoing Risk Assessment
Organizations must proactively and continuously assess risks and threats to their IT systems, taking reasonable, documented action to mitigate those risks and remain vigilant. - Report Cybersecurity Incidents Within 72 Hours
Covered entities must notify the Department of Public Service’s Office of Resilience within 72 hours of reasonably believing a cybersecurity incident has occurred, including incidents affecting third-party service providers that impact the covered entity’s IT systems or PII. - Third-Party Service Provider Requirements
Third-party vendors must contractually agree to notify covered entities of any cybersecurity incidents that directly impact the covered entity’s IT systems or nonpublic information. - Retain Cybersecurity Records for Five Years
All records related to cybersecurity events and incidents must be retained for a minimum of five calendar years and be available for regulatory review. - Grant DPS Audit Access
Department of Public Service staff must be granted physical and digital access to all covered entity assets upon request for the purpose of conducting cybersecurity audits and compliance reviews. - Annual Senior Management Certification
Senior management must annually certify compliance with the regulations to the Director of the DPS Office of Resilience, Utility Security, Nuclear Affairs, and Emergency Preparedness. - Incident Recovery Planning
Entities must maintain documented plans for recovery and restoration of normal operations in a safe and timely manner following a cybersecurity incident.
What Organizations Need to Do
Compliance with 16 NYCRR Part 1200 requires deliberate, documented action across governance, operations, and vendor management. Here are the key steps covered entities should take:
- Appoint or Verify Your CISO
Confirm that a qualified Chief Information Security Officer is formally designated, with clear authority and responsibility for cybersecurity governance and policy enforcement. - Conduct a Comprehensive IT Security Assessment
Engage in an IT Security Assessment to map all IT systems and data flows, and the effectiveness of your security controls. Conduct a pen test to identify vulnerabilities and threat vectors, especially those involving PII, and receive documented findings as the foundation of your cybersecurity program. - Build or Update Your Cybersecurity Program & Policies
Develop or update your formal cybersecurity program and written policies to align with Part 1200 requirements, including data governance, access controls, monitoring, and incident response. - Establish a 72-Hour Incident Notification Protocol
Create a thorough incident response plan, including an internal escalation and notification workflow capable of triggering DPS reporting within 72 hours of a suspected incident. Extend this requirement to key third-party vendors via contract. Conduct tabletop exercises to evaluate the incident response plan, ensuring it covers various scenarios and details how to respond efficiently. - Audit Your Third-Party Vendors
Review all service provider contracts to ensure cybersecurity incident notification obligations are included. Assess vendor security postures and require alignment with your program standards. - Implement a 5-Year Records Retention Policy
Establish or update records management procedures to ensure that all cybersecurity events, incidents, and related documentation are retained for a minimum of five calendar years. - Prepare for DPS Audits
Ensure DPS staff can be granted timely physical and digital access to systems for audit purposes. Designate a point of contact and document your compliance readiness - Schedule Annual Senior Management Certification
Establish a governance cadence ensuring senior leadership reviews, affirms, and submits the required annual Certification of Compliance to the Director of the DPS Office of Resilience. - Provide Employee Security Awareness Training
Ensure your employees are enrolled in annual security and awareness training to stay informed of how to maintain a secure and compliant environment, manage sensitive information, data privacy, and other regulatory requirements. Other compliance-specific training may also be required.
Timeline for Compliance
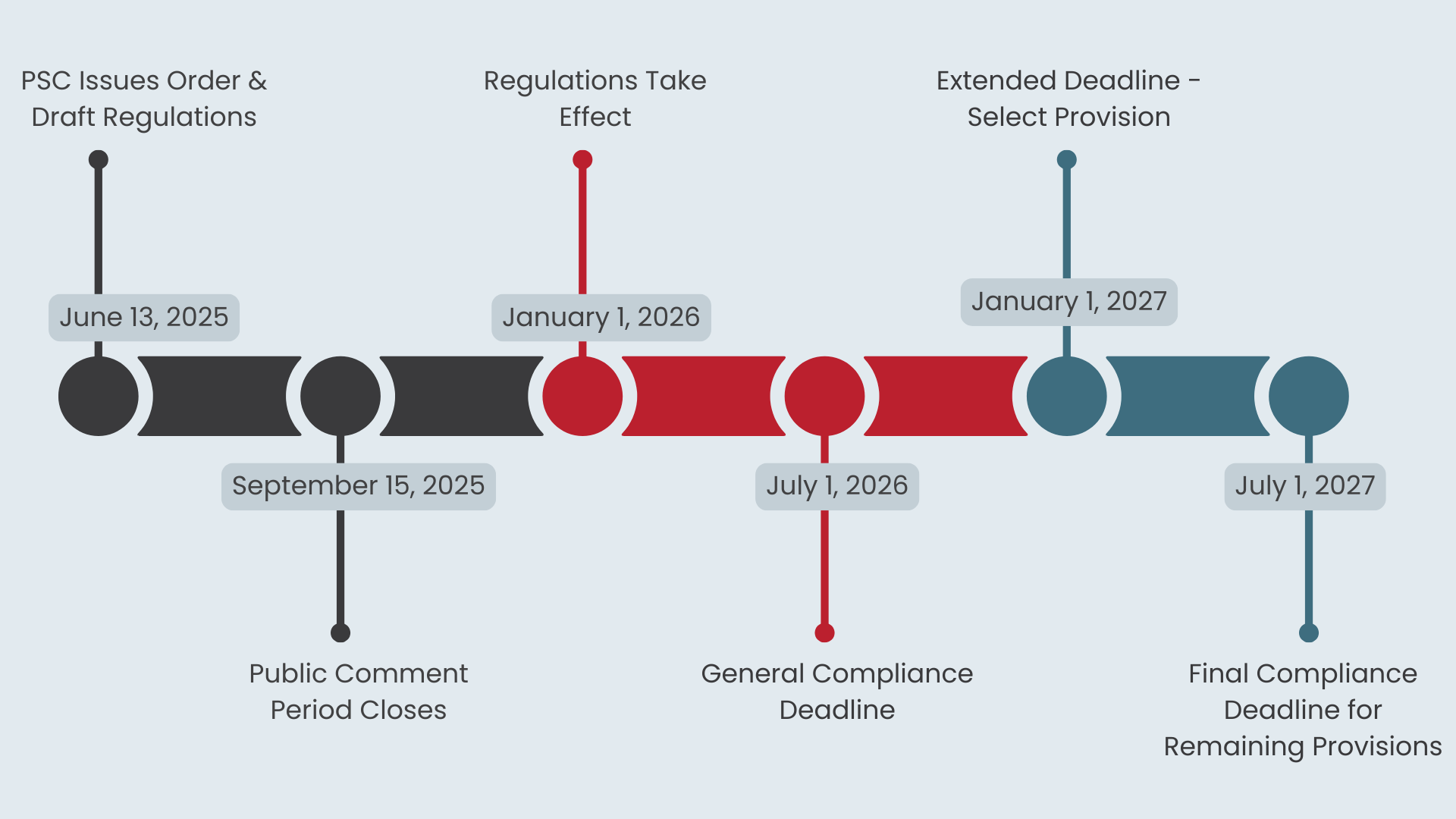
The regulations include a phased compliance schedule with staggered deadlines. Organizations should build their compliance roadmaps around the following milestones:
- June 13, 2025: PSC Issues Order & Draft Regulations
The PSC issues Case 25-M-0302, formally instituting the cybersecurity proceeding and publishing draft regulations for stakeholder comment. - September 15, 2025: Public Comment Period Closes
Interested parties and stakeholders submit comments on the draft regulations. The Commission reviews feedback and finalizes the rules. - January 1, 2026: Regulations Take Effect
16 NYCRR Part 1200 becomes effective. The compliance clock begins. Annual Certifications of Compliance are now required on an ongoing basis. - July 1, 2026 (180 Days): General Compliance Deadline
Covered entities must be in full compliance with most requirements of Part 1200, including CISO designation, cybersecurity program, written policies, incident reporting protocols, and records retention. - January 1, 2027 (One Year): Extended Deadline – Select Provisions
Compliance is required with sections 1200.4(b), 1200.5, 1200.9, 1200.12, and 1200.14(b), covering specific risk assessment, testing, and access management requirements. - July 1, 2027 (18 Months): Final Compliance Deadline for Remaining Provisions
All remaining provisions must be implemented. Full program maturity is expected across all covered entities. No further transitional accommodations after this date.
Final Thoughts
Case 25-M-0302 marks a genuine inflection point in how New York regulates utility cybersecurity. By treating cyber resilience as a core component of safe and adequate service, the PSC has elevated cybersecurity from a best practice to a legal mandate, with audit rights, incident reporting obligations, and senior-level accountability to back it up.
What’s particularly significant is the broader trajectory these requirements signal. The regulations explicitly describe IT and PII protection as a “first step,” with Operational Technology (OT), the systems that run physical infrastructure, expected to follow in a subsequent proceeding.
Organizations that wait for OT rules to act will find themselves far behind.
Emerging amid a federal landscape that has de-emphasized new regulatory burdens, New York’s actions send a clear message: cybersecurity accountability is expanding at the state level, and it is not optional.
Now is the time to invest in governance, documentation, and program maturity, before the next compliance deadline arrives.
CampusGuard is here to help you every step of the way, whether you are just starting to establish your cybersecurity program, through an IT security assessment, policy and procedure reviews, tabletop exercises to test your incident response plan, pen testing, third-party vendor reviews, and online security awareness and compliance training.
We are your trusted partner in boosting your cybersecurity posture and achieving compliance. Contact us today to learn more and get started!

