It’s not uncommon for people, especially those who are not deeply immersed in cybersecurity or IT operations, to confuse penetration tests (or pen tests for short) with vulnerability scans. Penetration tests and vulnerability scans complement each other by providing diverse perspectives on an organization’s security posture, but are not the same.
Penetration tests simulate real-world attacks to identify weaknesses and test defenses, via exploitation, while vulnerability scans focus on automated detection of known vulnerabilities. Together, they help organizations mitigate security risks and strengthen their overall cybersecurity defenses.
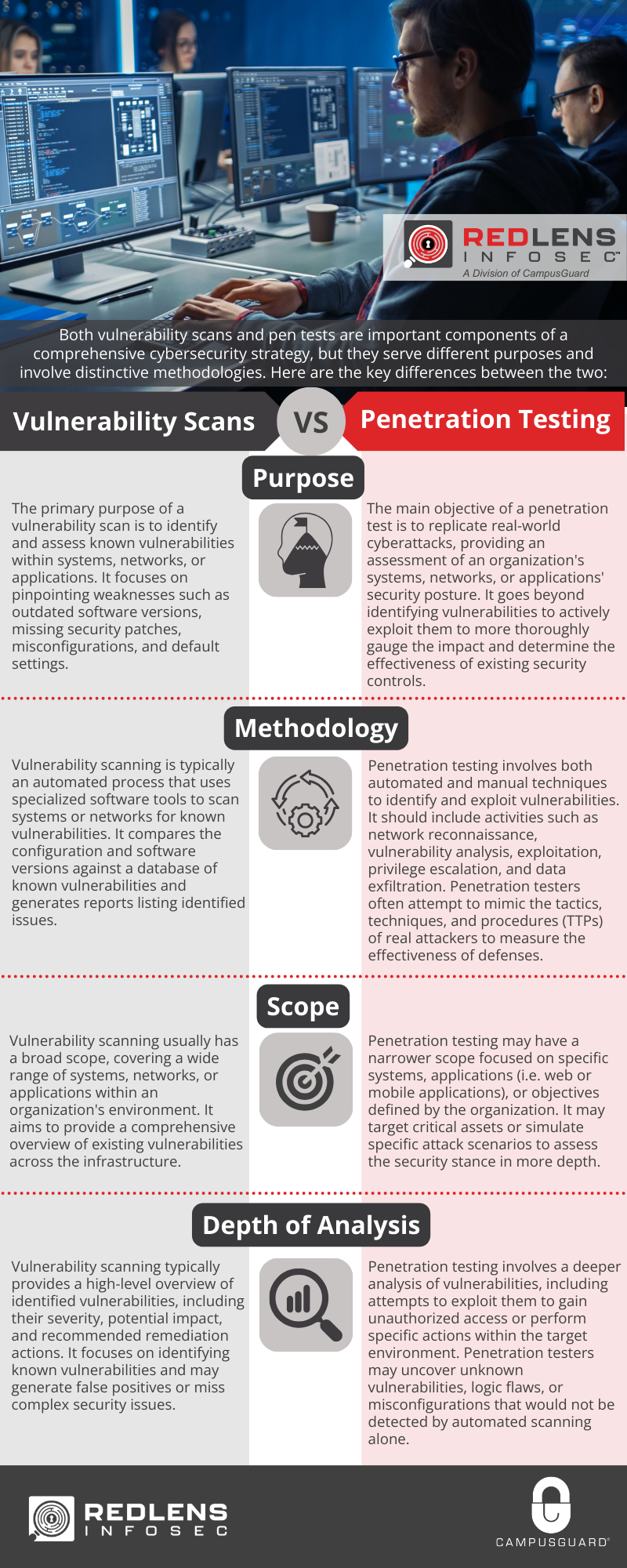
Both vulnerability scans and pen tests are important components of a comprehensive cybersecurity strategy, but they serve different purposes and involve distinctive methodologies. Here are the key differences between the two:
Purpose:
- Vulnerability Scan: The primary purpose of a vulnerability scan is to identify and assess known vulnerabilities within systems, networks, or applications. It focuses on pinpointing weaknesses such as outdated software versions, missing security patches, misconfigurations, and default settings.
- Penetration Test: The main objective of a penetration test is to replicate real-world cyberattacks, providing an assessment of an organization’s systems, networks, or applications’ security posture. It goes beyond identifying vulnerabilities to more thoroughly gauge the impact and determine the effectiveness of existing security controls.
Methodology:
- Vulnerability Scan: Vulnerability scanning is typically an automated process that uses specialized software tools to scan systems or networks for known vulnerabilities. It compares the configuration and software versions against a database of known vulnerabilities and generates reports listing identified issues.
- Penetration Test: Penetration testing involves both automated and manual techniques to identify and exploit vulnerabilities. It should include activities such as network reconnaissance, vulnerability analysis, exploitation, privilege escalation, and data exfiltration. Penetration testers often attempt to mimic the tactics, techniques, and procedures (TTPs) of real attackers to measure the effectiveness of defenses.
Scope:
- Vulnerability Scan: Vulnerability scanning usually has a broad scope, covering a wide range of systems, networks, or applications within an organization’s environment. It aims to provide a comprehensive overview of existing vulnerabilities across the infrastructure.
- Penetration Test: Penetration testing may have a narrower scope focused on specific systems, applications (i.e. web or mobile applications), or objectives defined by the organization. It may target critical assets or simulate specific attack scenarios to assess the security stance in more depth.
Depth of Analysis:
- Vulnerability Scan: Vulnerability scanning typically provides a high-level overview of identified vulnerabilities, including their severity, potential impact, and recommended remediation actions. It focuses on identifying known vulnerabilities and may generate false positives or miss complex security issues.
- Penetration Test: Penetration testing involves a deeper analysis of vulnerabilities, including attempts to exploit them to gain unauthorized access or perform specific actions within the target environment. Penetration testers may uncover unknown vulnerabilities, logic flaws, or misconfigurations that would not be detected by automated scanning alone.
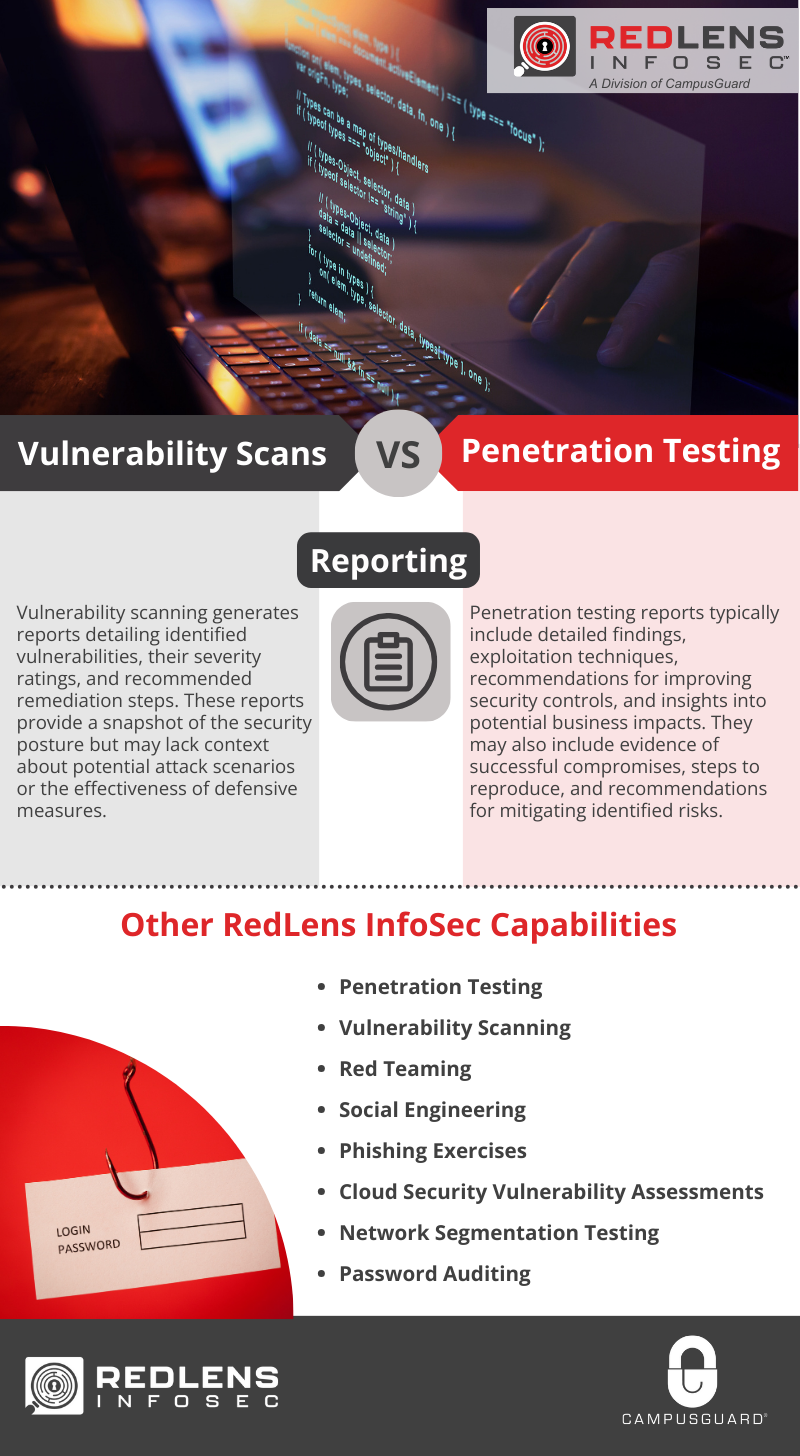
Reporting:
- Vulnerability Scan: Vulnerability scanning generates reports detailing identified vulnerabilities, their severity ratings, and recommended remediation steps. These reports provide a snapshot of the security posture but may lack context about potential attack scenarios or the effectiveness of defensive measures.
- Penetration Test: Penetration testing reports typically include detailed findings, exploitation techniques, recommendations for improving security controls, and insights into potential business impacts. They may also include evidence of successful compromises, steps to reproduce, and recommendations for mitigating identified risks.
While both vulnerability scanning and penetration testing are essential components of a robust cybersecurity program, they serve different purposes and provide collaborative insights into an organization’s security outlook.
No matter your security objectives or needs, RedLens InfoSec, CampusGuard’s trusted security division, offers vulnerability scanning, pen testing, and a host of additional service capabilities to fortify your organization’s IT security and compliance initiatives.
Additional feedback from our RedLens InfoSec team:
[Garten]: “With the differences between a vulnerability scan and a penetration test defined, the benefit of having both performed on your organization’s asset becomes clear. However, RedLens understands each client has their unique constraints and needs. That’s why RedLens InfoSec takes great pride in meeting customers where they are. New to cybersecurity scans and testing? We’re here to help navigate the waters to determine the best way to meet your needs. Are you a seasoned veteran of cybersecurity testing? We are eager and ready to challenge your defenses in new and novel ways. Regardless of where you are today, RedLens InfoSec is your partner in advancing your cybersecurity program for a more secure future.”
Quick Comparison: Penetration Testing vs. Vulnerability Scans